VMware has identified a security thread within vCenter. An upload vulnerability in vCenter’s Analytics service allows attackers to run arbitrary code on vulnerable servers. On a scale of 1 to 10 in terms of impact, the vulnerability, CVE-2021-22005, is rated 9.8. “The implications of this vulnerability are serious and it will only be a matter of time, probably minutes after the announcement, before working exploits appear,” VMware said on September 21. The thread has been registered by VMware under VMSA-2021-0002.
VMware has identified a security thread within vCenter. An upload vulnerability in vCenter’s Analytics service allows attackers to run arbitrary code on vulnerable servers. On a scale of 1 to 10 in terms of impact, the vulnerability, CVE-2021-22005, is rated 9.8. “The implications of this vulnerability are serious and it will only be a matter of time, probably minutes after the announcement, before working exploits appear,” VMware said on September 21. The thread has been registered by VMware under VMSA-2021-0002.
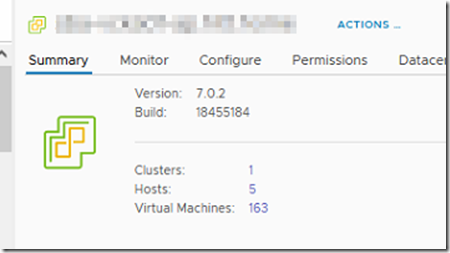
To mitigate the security issue you need to upgrade your vCenter instance to version 7.0U2d build 18455184.
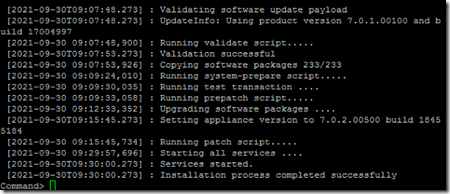
At a customer I am upgrading a vCenter from version 7.0.1.00100 to 7.0.2.00500. This version was released on September 16, VMware confirms in knowledge base article 85717 that this version fixes the above mentioned issue.
To install the update you need to logon to the vCenter Server Appliance Management Interface (VAMI). To access the VAMI you need to browse to https://vcenter.fqdn:5480. In the left side menu click on Update.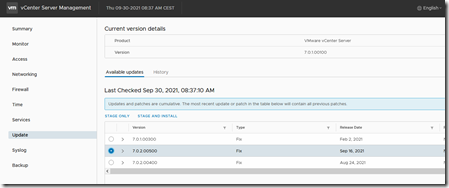 The vCenter updates are cumulative so click on the latest version (in this case that is version 7.0.2.00500), and click on “Stage and Install””.
The vCenter updates are cumulative so click on the latest version (in this case that is version 7.0.2.00500), and click on “Stage and Install””.
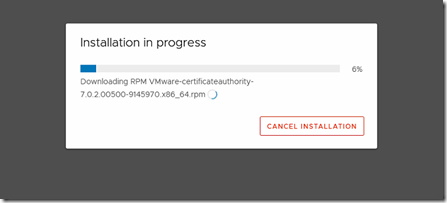
The update starts running.
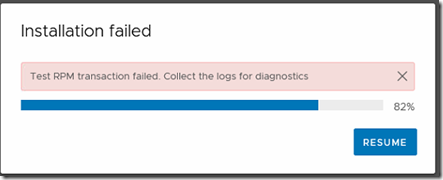
But after a couple of minutes the installation fails and the installation is stuck in an infinity loop.
To break trough this loop you need to close the browser and logon to the vCenter via SSH.
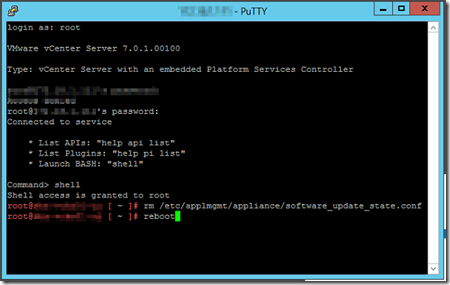
After you logon you enter “Shell” to launch the BASH (Unix) Shell. Enter to following command to delete the state file that is causing the loop.
“rn /etc/applmgmt/appliance/software_update_state.conf”
When the file is deleted you need to reboot the vCenter Appliance.
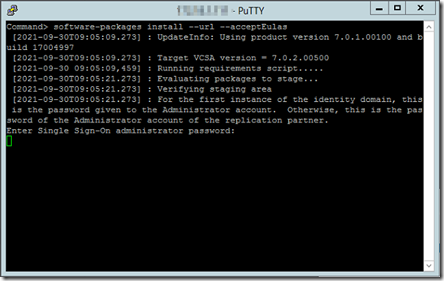
After the reboot you execute the following command from the appliance shell: “software-packages install –url –acceptEulas”. Next you are prompted to enter SSO password for the administrator@vsphere.local account.
After some patient waiting the message appears that the installation process was successful.
When you log back into vCenter you can confirm that vCenter is now upgraded and the security thread is mitigated.