Placing a VMware vSphere ESXi host in maintenance mode works the same whether the VMs run on vSAN or other types of attached storage. But if the VMs are running on vSphere on a Nutanix cluster the process of placing a host into maintenance mode does work a little different. This is because of the way Nutanix is working together with VMware vSphere ESXi. On every VMware vSphere ESXi host on Nutanix, there is a VM called Controller Virtual Machine (CVM). This VM controls and managed the storage usage. All the storage IO for a host goes through that CVM VM. Lees verder How to place a VMware vSphere ESXi host on Nutanix in maintenance mode
Categorie archieven: VMware
vSphere vCenter and NSX-T, Portgroup and Segment inventory out of sync

In a SDDC project the customer is requesting to rename the vLANS and vSphere vCenter Portgroups. Since the costomer is using NSX-T Datacenter the place to perform this rename is actions is the NSX-T Datacenter Manager console. The location where you can find this information is under Network>Segments. Or via the API.
Lees verder vSphere vCenter and NSX-T, Portgroup and Segment inventory out of sync
NSX-T Data Center required network ports
 In this blog post I will sum up all the network ports that are required to operate various capabilities that are within NSX-T Data Center. This blog is about current version of NSX-T Data Center, the current version is 3.2.0.0.1. Please acknowledge that not all features are available under each NSX-T Data Center Edition.
In this blog post I will sum up all the network ports that are required to operate various capabilities that are within NSX-T Data Center. This blog is about current version of NSX-T Data Center, the current version is 3.2.0.0.1. Please acknowledge that not all features are available under each NSX-T Data Center Edition.
Please verify which features are licensed for your deployment so you can check which features you can deploy under your license.
Setting up NSX Advanced Load Balancer for VMware Horizon
 Back in June 2019 VMware published a press report on there intent to acquire AVI Networks. AVI Networks was a leader in the multi-cloud application delivery services. VMware has rebranded the load balancing product, it is now called NSX Advanced Load Balancer.
Back in June 2019 VMware published a press report on there intent to acquire AVI Networks. AVI Networks was a leader in the multi-cloud application delivery services. VMware has rebranded the load balancing product, it is now called NSX Advanced Load Balancer.
In this article I will describe how to install the NSX Advanced Load Balancer, and configure it for VMware Horizon.
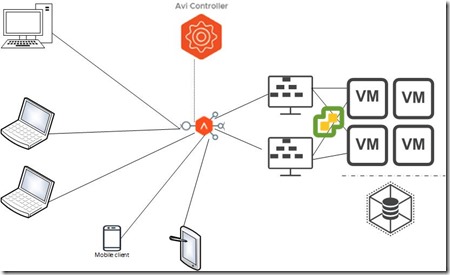
This is the architecture we are going to build.
Lees verder Setting up NSX Advanced Load Balancer for VMware Horizon
NSX-T Manager SSH Root Access Denied
We want to logon to access the NSX-T as root via Putty, when we try to logon we are presented with a Access Denied error.
To resolve this issue we perform the following procedure:
Access the NSX-T manager console via vCenter and logon with your root credentials.
vim /etc/ssh/sshd_config
Press “I” to access INSERT Mode
Change PermitRootLogin to yes
Change StrictModes to no
Press the ESC key to exit the INSERT Mode
Lees verder NSX-T Manager SSH Root Access Denied
Workspace ONE Access account error
 Workspace ONE access (the product formerly known as VMware Identity Manager) is a part of VMware End User Computing products.
Workspace ONE access (the product formerly known as VMware Identity Manager) is a part of VMware End User Computing products.
Workspace ONE combines the user’s identity with factors such as device and network information to make intelligence-driven, conditional access decisions for applications delivered by Workspace ONE.
Lees verder Workspace ONE Access account error
A generic error occurred in the vSphere Replication Management Server
 At a customer site where the vSphere environment is setup over two locations. At both location the customer has setup MSA storage.
At a customer site where the vSphere environment is setup over two locations. At both location the customer has setup MSA storage.
In order to keep the customer data safe we want to setup replication between the two locations. To set this up we install VMware vSphere Replication.
Lees verder A generic error occurred in the vSphere Replication Management Server
VMware vCenter upgrade, Test RPM transaction failed
 VMware has identified a security thread within vCenter. An upload vulnerability in vCenter’s Analytics service allows attackers to run arbitrary code on vulnerable servers. On a scale of 1 to 10 in terms of impact, the vulnerability, CVE-2021-22005, is rated 9.8. “The implications of this vulnerability are serious and it will only be a matter of time, probably minutes after the announcement, before working exploits appear,” VMware said on September 21. The thread has been registered by VMware under VMSA-2021-0002.
VMware has identified a security thread within vCenter. An upload vulnerability in vCenter’s Analytics service allows attackers to run arbitrary code on vulnerable servers. On a scale of 1 to 10 in terms of impact, the vulnerability, CVE-2021-22005, is rated 9.8. “The implications of this vulnerability are serious and it will only be a matter of time, probably minutes after the announcement, before working exploits appear,” VMware said on September 21. The thread has been registered by VMware under VMSA-2021-0002.
Lees verder VMware vCenter upgrade, Test RPM transaction failed
File locks on vSphere
 In a project we where starting an action to export a VM to an OVF file. We launched the export from the vSphere WebClient. During the export action the file stream failed and we cancelled the export action. Because we where running into a time restriction with the allowed time frame we wanted to boot the machine so it would be available to the end users.
In a project we where starting an action to export a VM to an OVF file. We launched the export from the vSphere WebClient. During the export action the file stream failed and we cancelled the export action. Because we where running into a time restriction with the allowed time frame we wanted to boot the machine so it would be available to the end users.
Lees verder File locks on vSphere
Reset VMware ESXi root password
 The root account is the only login account to vSphere ESXi. There is no extra account to create a backdoor to logon to vSphere ESXi when the root password is lost. When a vSphere ESXi host is added to a vCenter instance, management of the host is primary done via vCenter. Troubleshooting ESXi is done primarily on the command line via an SSH connection. By default the SSH service is stopped. To start the SSH service you have to access the server via vCenter Host>Configure>System>Services. When you don’t have the root password for the vSphere ESXi host you have to follow the following procedure.
The root account is the only login account to vSphere ESXi. There is no extra account to create a backdoor to logon to vSphere ESXi when the root password is lost. When a vSphere ESXi host is added to a vCenter instance, management of the host is primary done via vCenter. Troubleshooting ESXi is done primarily on the command line via an SSH connection. By default the SSH service is stopped. To start the SSH service you have to access the server via vCenter Host>Configure>System>Services. When you don’t have the root password for the vSphere ESXi host you have to follow the following procedure.
Lees verder Reset VMware ESXi root password